Customer data is the lifeblood of modern business. Every purchase, support request, or account registration generates information that helps companies improve services and build long-term relationships with their customers. At the same time, this data has become one of the most sensitive assets an organization holds — and one of the most attractive targets for cybercriminals.
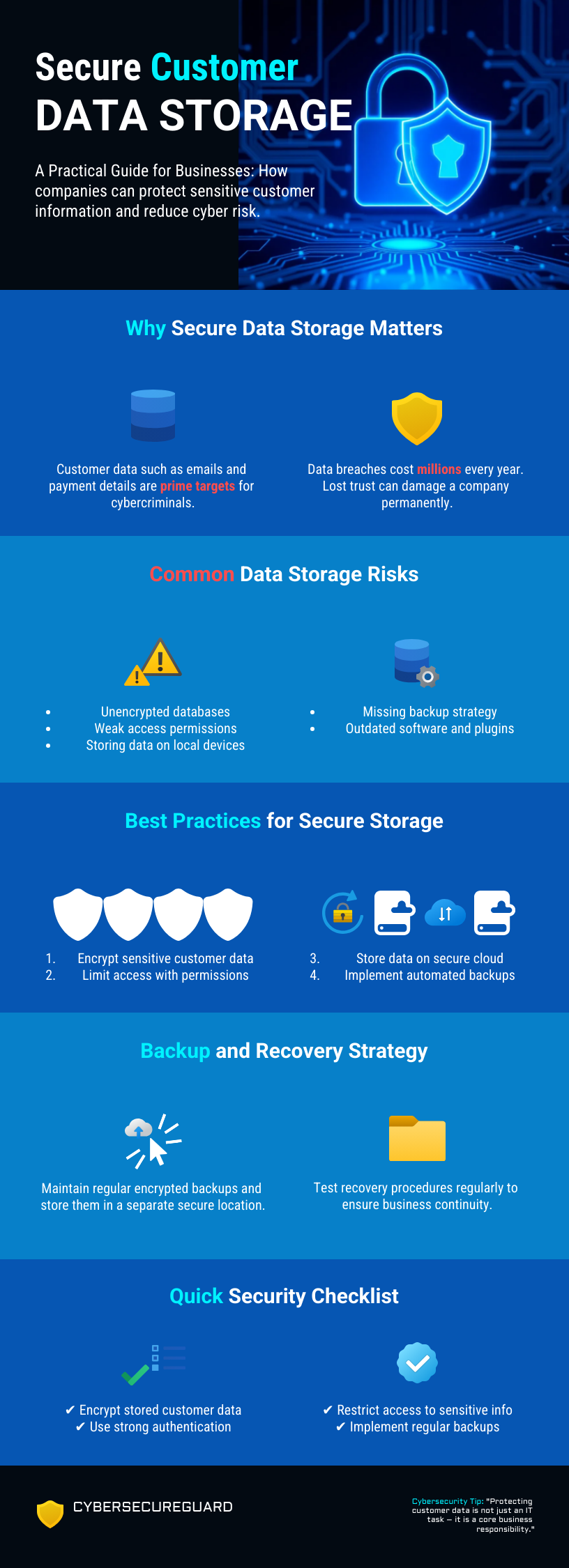
A single misconfigured database, an unencrypted backup, or overly broad access permissions can expose thousands of customer records. The consequences can include regulatory penalties, legal claims, and long-term reputational damage. Securely storing customer data therefore requires more than basic IT protection. Businesses need strong encryption, strict access controls, secure backup strategies, and compliance with modern data protection regulations.
This guide explains the key principles of secure customer data storage in 2026, covering both technical safeguards and practical steps businesses can take to reduce risk and protect customer trust.
1. Why Secure Storage Matters More Than Ever
Regulations like GDPR, CCPA, and ISO 27001 have set a clear expectation: businesses that collect customer data are legally and ethically responsible for protecting it. GDPR alone can impose fines of up to €20 million or 4% of global annual turnover — whichever is higher. But compliance alone is not the goal. A company can tick every regulatory checkbox and still suffer a devastating breach if the underlying security posture is weak. Genuine data security means your customers’ information is safe even if attackers breach your perimeter — and that requires going well beyond minimum legal requirements.
The threat landscape has evolved dramatically over the past decade. Attackers no longer rely solely on complex, targeted intrusions. Much of today’s risk comes from basic, preventable mistakes: publicly exposed databases, storage buckets left open to the internet, unencrypted backup files stored in accessible locations, or service accounts granted far more permissions than they need. Automated scanning tools continuously probe the internet for exactly these kinds of misconfigurations — and they find them within minutes of their creation. High-profile breaches at well-known companies have repeatedly originated not from sophisticated zero-day exploits, but from a single overlooked configuration error.
Insider threats are equally significant and often underestimated. Not every data incident is caused by an external attacker. Disgruntled employees, contractors with overly broad access rights, or simply well-meaning staff who make a mistake can all result in customer data being exposed, exfiltrated, or accidentally deleted. A strong data security strategy must account for threats from within the organisation just as rigorously as those coming from outside.
It is also worth understanding what attackers actually do with customer data once they have it. Stolen records are sold on dark web marketplaces, used for identity theft and account takeover attacks, leveraged for phishing campaigns against your customers, or held for ransom. The damage therefore extends far beyond your own organisation — your customers bear the direct consequences of your security failures. This is what makes secure data storage not just a technical concern, but a fundamental ethical obligation.
Critical misconception: Many companies believe their cloud provider handles data security for them. In reality, cloud providers operate under a shared responsibility model — they secure the physical infrastructure and the availability of their services, but you are fully responsible for securing the data you store within them, including access controls, encryption, and configuration.
2. Encryption: The Non-Negotiable Foundation
Encryption is one of the most important ways to protect customer data. Even if attackers gain access to your systems, encrypted data cannot be used without the correct decryption keys. In other words, encryption can turn stolen data into useless information. However, encryption only works if it is implemented correctly. A common mistake is to encrypt only the hard drive and assume the data is fully protected. In reality, security needs to work in several layers. You must consider who can access the data at the application level, the database level, and the storage level. Each of these layers should have its own protection. When securing data, businesses must always protect two situations: data at rest and data in transit.
Encryption at Rest
All stored customer data should be encrypted. This includes databases, backups, log files, file systems, and object storage. The most common and trusted encryption standard today is AES-256 (Advanced Encryption Standard with a 256-bit key). It is widely supported by operating systems, databases, and cloud providers. Sensitive data should never be stored in plain text. This also applies to internal systems or test environments. Many organisations forget that development or staging systems can also be attacked. In fact, attackers often target these systems because security controls are weaker there.
Full-disk encryption is a good basic protection, especially against hardware theft or lost devices. However, it does not protect data if an attacker gains access to a running system. For this reason, it is recommended to also use column-level or field-level encryption for sensitive data such as personally identifiable information (PII). Even if the database is compromised, the protected fields remain unreadable without the correct key.
Encryption in Transit
Data must also be protected while it moves between systems. This includes communication between users, servers, databases, and external services. All connections should use TLS encryption. Today, TLS 1.2 is the minimum standard, while TLS 1.3 is preferred because it offers stronger security and better performance. Businesses should enforce HTTPS on all systems. Unencrypted HTTP connections should never be allowed, even on internal networks. Adding HTTP Strict Transport Security (HSTS) headers helps ensure that browsers only use secure connections.
Older protocols such as SSLv3, TLS 1.0, and TLS 1.1 should be disabled because they are known to have security weaknesses. For internal system communication, especially in microservices environments, mutual TLS (mTLS) is recommended. With normal TLS, only the server proves its identity. With mTLS, both systems must authenticate each other. This greatly reduces the risk of unauthorized services communicating inside your infrastructure. Modern service mesh tools such as Istio or Linkerd can automatically enforce mTLS across many services.
Key Management
Encryption is only secure if the encryption keys are properly protected. One of the most common mistakes is storing encryption keys in the same location as the data they protect. If an attacker can access both, the encryption becomes useless. Businesses should use a dedicated Key Management Service (KMS). Examples include AWS KMS, Azure Key Vault, or HashiCorp Vault. These systems securely store keys, manage key rotation, and keep detailed logs of how keys are used. Encryption keys should never be stored directly in source code, configuration files, or environment variables that could be exposed in a repository.
It is also important to rotate keys regularly. A common practice is rotating data encryption keys every 90 days, while key encryption keys are rotated once per year. Older keys should remain available long enough to decrypt existing data, but they should no longer be used to encrypt new information. Finally, businesses should define a key recovery process. If the key management system becomes unavailable, the organisation must still be able to safely restore access to encrypted data without creating new security risks.
3. Access Control & the Principle of Least Privilege
Encryption protects customer data when it is stored. However, access control protects data while it is being used. Even strongly encrypted data can be exposed if the wrong people or systems are allowed to access it. One of the biggest risks inside organisations is overprivileged accounts. This means a user or service has more permissions than necessary. Sometimes this happens by accident when permissions are added over time and never removed. In other cases, an attacker may use these permissions to access sensitive information.
To reduce this risk, organisations should follow the Principle of Least Privilege (PoLP). This principle means that every person, system, or process should only have the minimum access needed to do its job — no more and no longer than necessary. In practice, maintaining this principle requires continuous attention. Access rights often grow over time when employees change roles, projects evolve, or temporary permissions become permanent. For this reason, companies must actively manage and review access control. Effective implementation of the Principle of Least Privilege usually includes the following practices:
Use Role-Based Access Control (RBAC).
Define clear roles for teams and systems, and assign permissions based on those roles. Each role should only allow access to the data needed for that specific task. Whenever organisational structures change, these roles and permissions should be reviewed.
Separate read and write permissions.
Most employees and services only need to read customer data. They do not need permission to modify or delete it. Write access should only be given when there is a clear operational need.
Require Multi-Factor Authentication (MFA).
All accounts that can access production systems or customer data should use MFA. This includes administrators, engineers, and automated deployment systems. Hardware security keys based on FIDO2 or WebAuthn provide stronger protection than SMS-based codes, which can be vulnerable to SIM-swapping attacks.
Review access regularly.
Companies should perform formal access reviews at least once every quarter. When employees leave the company or change roles, their access permissions should be updated immediately. Accounts that belong to former employees are a common entry point for attackers.
Use temporary credentials instead of permanent keys.
Long-term passwords or API keys create unnecessary risk. Modern systems can generate temporary credentials that automatically expire. Examples include AWS IAM temporary credentials or dynamic secrets provided by tools like HashiCorp Vault.
Log and monitor all data access.
Every action involving customer data — reading, modifying, or deleting information — should be recorded in an audit log. These logs should include the time of the action, the user or system identity, and the context of the request. Reliable audit logs help detect suspicious activity and provide important evidence during security investigations.
4. Data Classification and Minimization
You cannot protect what you have not categorised. Before you can apply appropriate security controls to customer data, you need to understand exactly what types of data you hold, where it lives, and how sensitive it is. Many organisations discover during their first data audit that they are storing far more personal information than they realised — in log files, debug outputs, email archives, or legacy databases that nobody actively maintains. A formal data classification framework is the foundation for everything else.
A standard four-tier model works well for most organisations: public data (no restrictions), internal data (not intended for outside parties), confidential data (personal information, business-sensitive records), and highly sensitive data (financial details, health records, authentication credentials). Each tier should have clearly documented handling requirements, access controls, retention periods, and disposal procedures.
Equally important — and often neglected — is data minimization. The principle is simple: collect only the data you absolutely need, retain it only for as long as necessary, and delete it securely and verifiably when it is no longer required. Every data field you collect is a field that can potentially be breached, subpoenaed, or misused. Organisations often accumulate data out of habit or vague future intent — “we might need this someday” — without a clear business justification.
GDPR explicitly requires a lawful basis for every category of personal data you process, and “it might be useful later” does not qualify. Conduct a regular data inventory and challenge every field: do we need this? why? for how long? who can access it? Implement automated retention policies that delete or anonymise data when its retention period expires, rather than relying on manual processes that are easy to forget.
5. Securing Databases and Backups
Databases are one of the most important parts of a company’s IT infrastructure because they often store large amounts of customer information. If attackers gain access to a database, they may be able to steal many customer records at once. For this reason, databases are a very common target in cyber attacks.
Unfortunately, many companies still make simple security mistakes. Some databases are accidentally accessible from the public internet. Others still use default ports or weak login credentials. In some cases, development or testing databases even contain real customer data because it is more convenient for developers. These situations create serious security risks and can lead to data breaches.
To protect customer data, databases should always run inside a private network environment, for example inside a Virtual Private Cloud (VPC). Only specific application servers or trusted systems should be allowed to connect to the database. All other connections should be blocked by default. This greatly reduces the risk of unauthorized access.
It is also important to remove default accounts and change default ports. Attackers often scan the internet for common database ports such as 3306 for MySQL, 5432 for PostgreSQL, or 27017 for MongoDB. They also try common usernames and passwords. Changing these settings does not solve every security problem, but it can prevent many simple automated attacks.
Monitoring also plays an important role in database security. Databases should record login attempts and important queries. By analysing these logs, companies can detect unusual activity. For example, a large data export during the night or many unexpected queries could be an early sign of a security incident.
Backups are another critical part of data protection. All backup files should be encrypted so that they cannot be read if someone gains access to them. The encryption keys used for backups should be stored separately from the main database keys. In addition, backups should be stored in a different location, such as another cloud region, so that data can still be recovered if the main system fails or is compromised.
Companies should also test their backups regularly. A backup is only useful if the data can actually be restored. During these tests, organisations should verify that the recovery process works correctly and that no important data is missing. Many companies only discover problems with their backups when a real incident happens.
Finally, businesses should keep at least one offline or isolated backup of their most important data. Ransomware attacks often try to encrypt both the main systems and connected backups. If backups are stored offline or in protected storage, attackers cannot easily reach them. This ensures that the company still has a reliable way to recover its data after an attack.
6. Security Compliance and Incident Response Strategies
Secure storage of customer data is not something you implement once and then forget. Security must be maintained and reviewed regularly. Systems change over time, new employees join the company, and new threats appear. Because of this, security controls must be checked and improved continuously.
Many data protection laws require this kind of ongoing security work. For example, GDPR Article 32 requires organisations to use appropriate technical and organisational measures to protect personal data. It also requires companies to regularly test and evaluate their security controls. Another well-known framework is ISO/IEC 27001, which focuses on building a complete Information Security Management System (ISMS). This includes written security policies, risk assessments, internal audits, and regular management reviews. Following these frameworks is not only about avoiding legal penalties. They also help companies build a structured and reliable approach to cybersecurity.
Every organisation that stores customer data should also have a clear incident response plan. This plan describes what to do if a data breach or security incident occurs. It should explain how a possible breach is detected and who must be informed immediately. It should also define internal communication steps so that legal teams, management, and communication teams can react quickly.
Legal reporting requirements are also important. Under GDPR, organisations must inform the responsible data protection authority within 72 hours after discovering a breach that could affect individuals. If the breach creates a high risk for customers, the company must also inform the affected people directly. Preparing communication templates in advance can help ensure that messages to customers are clear and accurate during a stressful situation.
Another important part of data security is continuous auditing. Companies should collect logs from all systems that process customer data. This includes databases, application servers, authentication systems, and cloud services. These logs can be analysed with a Security Information and Event Management (SIEM) system to detect suspicious activity.
Monitoring systems should create alerts for unusual behaviour. Examples include repeated login failures, sudden access to sensitive data, large data exports, or unexpected changes to security settings. These alerts help security teams detect problems early. It is also important that security logs cannot be changed or deleted easily. Logs should be stored in a secure system that protects them from manipulation. Many organisations keep these logs for at least 12 months to meet legal and regulatory requirements.
In addition to monitoring, companies should regularly test their security. Penetration tests and vulnerability scans can help identify weaknesses in databases, storage systems, and infrastructure. These tests should be performed at least once per year and also after major system changes. The results should be documented and used to improve the company’s overall security strategy.
Conclusion: How to securely store customer data for businesses
Securely storing customer data is no longer just a technical task for IT departments — it is a fundamental responsibility for every modern business. As organizations increasingly rely on digital systems, cloud platforms, and customer analytics, the amount of sensitive data being processed continues to grow. Without proper protection, this data can quickly become a major security risk.
Businesses that understand how to securely store customer data take a proactive approach to cybersecurity. This includes implementing strong encryption, enforcing strict access control policies, protecting backups, and regularly reviewing their security configurations. Just as important is maintaining compliance with data protection regulations and ensuring that employees understand their role in safeguarding sensitive information.
Ultimately, secure customer data storage is not only about preventing breaches. It is about maintaining trust, protecting your reputation, and demonstrating that your organization takes data protection seriously. Companies that invest in proper data security today are far better prepared to operate safely in an increasingly complex and hostile digital landscape.
I recommend you read the following articels:
Backup Exists – But Data Cannot Be Restored When It Matters Most
How to Build a Simple and Effective Cybersecurity Plan for Your Team
How to Protect Your Company’s Mobile Phones and Laptops from Cyber Threats




