Security in small and mid-sized environments is often not the result of a deliberate decision. It is simply what is already in place. Microsoft Defender runs by default, requires little setup, and creates no extra cost, so it often feels sufficient. As long as everything works, there is no reason to question it.
Cybersecurity issues, however, rarely begin in an obvious way. They start with uncertainty. An alert appears, a system behaves differently, and it is not clear what is actually happening or what action is required. In that moment, the real question is not whether antivirus is installed, but whether the situation is understood and handled fast enough.
This article explains where Microsoft Defender works well, where its limits are, and why solutions like CrowdStrike become relevant when security turns into a real business concern.
Why Microsoft Defender Feels “Enough”
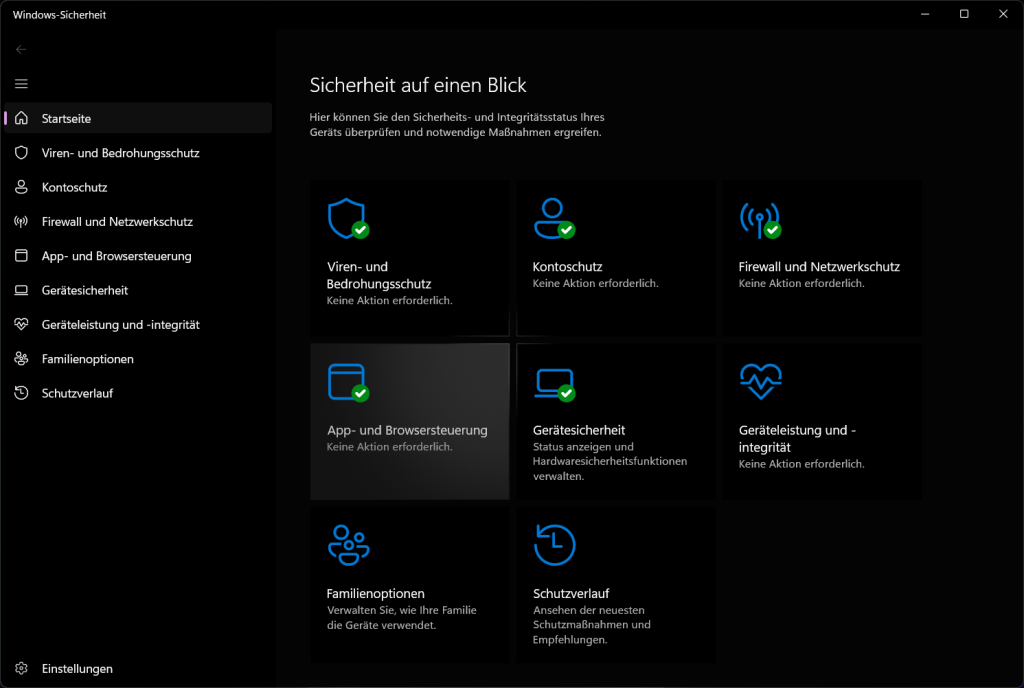
Microsoft Defender comes pre-installed on almost every Windows system, which means that for many small and mid-sized businesses, security is already “there” from day one — no additional solution to evaluate, no extra budget to justify, no complex onboarding process to manage. It runs quietly in the background, updates automatically, and integrates seamlessly into the Microsoft environment that most SMEs already rely on. From a practical standpoint, this feels like the ideal setup: convenient, cost-efficient, and delivering the impression of built-in protection without any extra effort. In daily business, it leads to a conclusion that feels entirely reasonable — “We are protected. We don’t need anything else.”
And to be fair, that assumption is not completely wrong. Microsoft Defender has improved significantly over the years. It performs well in independent lab tests and is capable of detecting a wide range of common threats. For basic protection, it does its job.
But this is precisely where the misunderstanding begins. What performs well in controlled environments does not always reflect real-world conditions. Most cyber incidents are not clean, predictable, or straightforward to detect — they are fast-moving, ambiguous, and often only recognisable in hindsight. The distinction that matters here is not about product quality; it is about scope. Baseline protection is designed to prevent known threats. Business-grade security is designed to help you understand and control a situation when something unexpected is already unfolding. Many SMEs only discover this difference when they are already under pressure — and by then, the cost of that gap becomes very real.
Where Microsoft Defender Reaches Its Limits
In real attack scenarios, the key question is not whether antivirus is installed. The real question is whether a business can detect and respond fast enough when something goes wrong. This is where many SMEs start to see the limits of Microsoft Defender. Defender is able to detect many threats, but detection alone is not enough in a real incident. The bigger challenge is understanding what is actually happening inside the systems.
1. Limited Visibility in Real Incidents
Microsoft Defender can detect many threats, but detection alone does not automatically provide a clear understanding of what is actually happening during an incident. In real situations, alerts often appear without full context, and this makes it difficult to see the bigger picture. When something unusual happens, businesses are faced with uncertainty. An alert may indicate suspicious activity, but it does not always explain how the situation developed or how serious it is. This leads to important questions that are not easy to answer without deeper expertise.
Teams need to understand which system was affected first, whether any data was accessed or moved, and if the attacker is still active in the environment. They also need to know if the issue is isolated or if it has already spread to other systems. Without this level of insight, it becomes difficult to assess the real impact of the incident. In many SMEs, there is no dedicated security team to investigate these questions in detail. As a result, decisions are often delayed or based on incomplete information. This increases the risk of reacting too slowly or taking the wrong actions. Limited visibility does not just create confusion, it directly affects response time and confidence. When the situation is not clear, every step takes longer. And in cybersecurity, delays can turn a manageable incident into a much more serious problem.
2. Detection vs. Response Gap
Detection alone does not stop an attack. This is one of the most common misunderstandings in small and mid-sized businesses. A system may detect something unusual and generate an alert, but that does not automatically mean the situation is under control. In many real incidents, problems escalate because alerts are missed, misunderstood, or not taken seriously. Teams may not know how to interpret the information, or they are unsure what steps to take next. In other cases, there is simply no clear response process in place, so valuable time is lost while people try to figure out what to do.
This creates a gap between detection and response. The system may recognize that something is wrong, but the business is not prepared to act quickly and effectively. And this gap is often where small incidents turn into serious problems. For SMEs, the issue is usually not a lack of tools. In many cases, the tools are already there. The real challenge is the lack of response capability. Without a clear plan, defined steps, and confidence in decision-making, even good detection does not lead to effective protection.
3. Configuration Complexity
While Microsoft Defender can be a powerful security solution, especially in larger enterprise environments, it does not work at its full potential out of the box. To be truly effective, it requires proper configuration, structured policy management, and continuous monitoring. In many small and mid-sized businesses, this level of setup is difficult to maintain. There is often limited time, limited internal expertise, and no dedicated security team. As a result, systems are left in their default state, and important features are not fully used.
At first, this may not seem like a problem. Everything appears to work, and no obvious issues are visible. But in reality, this often leads to incomplete protection. Security policies may not be enforced consistently, alerts may not be reviewed in detail, and potential risks remain unnoticed. This creates a false sense of security. The tool is in place, but it is not configured in a way that matches the actual risk of the business. And because there are no immediate signs of failure, this gap often remains hidden until a real incident occurs.
A detailed step-by-step approach can be found in our guide on optimally setting up Windows Defender for small business environments.
What Makes CrowdStrike Different
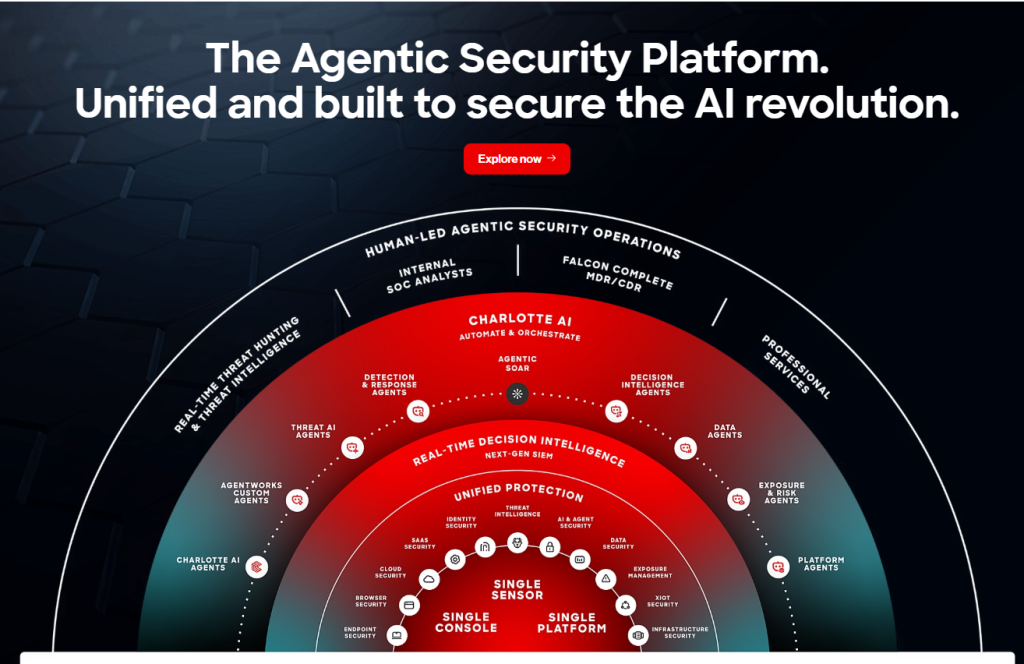
CrowdStrike is not just an antivirus replacement. It is designed as an endpoint detection and response platform, also known as EDR, and this changes how security works in practice. Traditional antivirus solutions mainly focus on preventing known threats. They try to block malicious files or detect patterns that are already documented. This approach works well for many common attacks, but it has limits when threats are new, more complex, or do not behave in a typical way.
CrowdStrike takes a different approach. Instead of only focusing on prevention, it is built around continuous visibility and fast response. It assumes that not every threat can be stopped in advance and that understanding what is happening in real time is just as important as blocking an attack.
This means the platform does not only answer the question “Is there a threat?” It also helps answer more important questions such as what is happening on the system, how the situation is developing, and what actions need to be taken next. For SMEs, this difference is critical. It shifts security from a passive setup that runs in the background to an active system that supports decision-making during an incident. This makes it easier to react quickly, reduce uncertainty, and keep control when something unexpected happens.
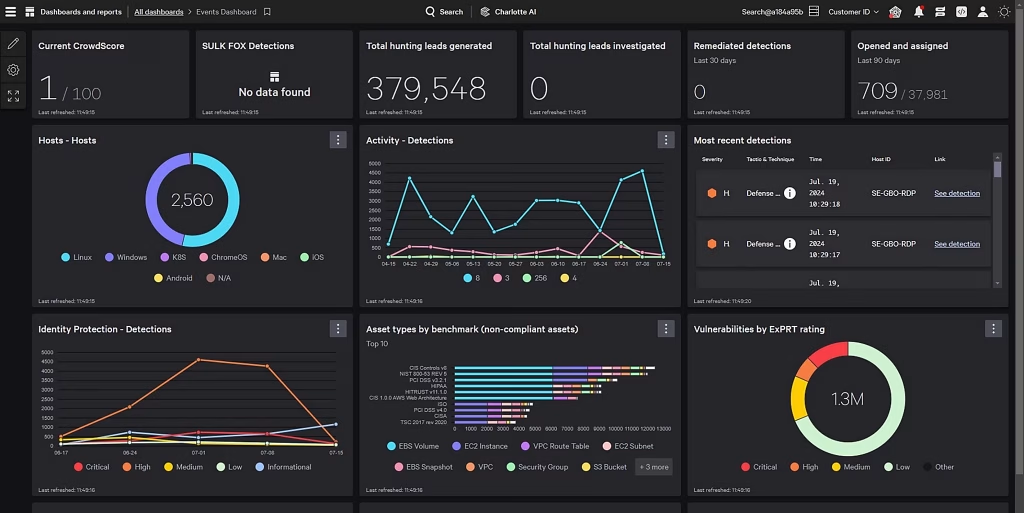
1. Real-Time Threat Visibility
One of the biggest advantages of CrowdStrike is real-time threat visibility. Instead of only showing that something suspicious has been detected, the platform helps businesses understand what is actually happening in their environment. When an incident occurs, it provides clear insight into how an attack started, what the attacker is doing at the moment, and which systems are affected. This creates a much more complete picture compared to simple alerts or isolated warnings.
In many situations, this clarity makes a critical difference. Without visibility, teams are forced to guess or react step by step without knowing the full scope of the problem. With real-time insight, they can see the situation more clearly and make informed decisions. For SMEs, this is especially important because there is often no large security team available. Decisions need to be made quickly and with limited resources. When the information is clear and easy to understand, response becomes faster and more effective. In this context, visibility is not just a technical feature. It directly supports decision-making and helps businesses stay in control during an incident.
2. Behavior-Based Detection
Another key difference of CrowdStrike is its focus on behavior-based detection. Instead of relying mainly on known signatures, the platform looks at how processes behave and how activity develops over time. Traditional antivirus solutions often depend on known patterns. They compare files or actions against a database of known threats. This works well for attacks that are already documented, but it becomes less effective when attackers use new techniques or slightly change their methods.
CrowdStrike takes a different approach by analyzing suspicious behavior, attack patterns, and unusual system activity. It looks at how processes interact, how commands are executed, and whether activity fits normal system behavior. This allows the platform to detect threats even when they are not yet known or do not match a specific signature.
This approach is especially important for modern threats. Ransomware often spreads quickly and changes its behavior. Zero-day attacks are, by definition, unknown at the time they occur. Fileless malware operates without traditional files and can bypass many classic detection methods. By focusing on behavior instead of only known signatures, CrowdStrike is better equipped to identify these types of threats early. For SMEs, this means a higher chance of detecting advanced attacks before they cause serious damage.
3. Fast and Structured Response
Another important strength of CrowdStrike is its ability to support fast and structured response during an incident. When something happens, the platform does not only detect the problem, it also helps guide the next steps. Instead of reacting without a clear plan, businesses can take immediate and targeted actions. Affected systems can be isolated to prevent the spread of an attack, malicious processes can be stopped quickly, and the overall impact can be understood in a short time.
This structured approach makes a significant difference in real situations. Without it, teams often lose valuable time trying to understand what to do first. Actions may be delayed, or the wrong priorities may be set, which can allow an incident to grow. For SMEs, this is where the biggest advantage becomes visible. There is usually no dedicated incident response team, and decisions need to be made quickly under pressure. When the platform supports clear and practical steps, it reduces uncertainty and helps businesses stay in control. In this context, response is not just about reacting. It is about reacting in a structured and effective way when time matters most.
4. Designed for Real-World Attacks
CrowdStrike is built around a different core assumption than traditional antivirus solutions. It does not assume that all attacks can be prevented. Instead, it is designed with the understanding that attacks will happen and that detection and response must be immediate. This mindset reflects how modern cyber threats work in reality. Attacks are often fast, unpredictable, and do not follow a simple pattern. They may bypass traditional defenses, use legitimate system tools, or evolve while they are already active inside a network.
Traditional antivirus focuses mainly on prevention. It tries to block threats before they enter the system. While this is important, it is not always enough in real-world scenarios where not every attack can be stopped in advance. CrowdStrike takes a more practical approach. It prepares businesses not only to prevent threats, but also to detect them early and respond quickly when something unexpected happens. This reduces the time attackers can operate inside a system and limits potential damage. For SMEs, this shift in mindset is critical. It moves security from a “we hope nothing happens” approach to a model where the business is prepared to act when it matters most.
Microsoft Defender vs. CrowdStrike: The Practical Difference
Here is the decision simplified:
| Aspect | Microsoft Defender | CrowdStrike |
|---|---|---|
| Setup | Easy, built-in | Requires onboarding |
| Protection Level | Baseline | Advanced |
| Visibility | Limited | High |
| Threat Detection | Good | Advanced + behavioral |
| Response Capability | Limited | Strong |
| Ideal For | Basic protection | Business-critical environments |
So… Is Microsoft Defender Enough?
The answer depends on your specific situation. There is no single solution that fits every business, and in some cases, Microsoft Defender can be enough. For very small setups with limited complexity, the built-in protection may provide a reasonable starting point. If only a few systems are in use, processes are simple, and there is little exposure to external risk, the overall threat level can be lower.
It can also be sufficient if no sensitive data is involved. Businesses that do not store client information, financial data, or critical internal documents often face fewer consequences in case of an incident. In these situations, the impact of a potential attack may be more limited. Another factor is risk tolerance. Some businesses are willing to accept a higher level of uncertainty. They understand that their setup is basic, but they choose to operate this way because the perceived risk is low or because security is not a current priority.
In addition, the absence of compliance requirements can influence the decision. If there are no regulatory obligations, no industry standards to meet, and no external audits, the pressure to implement advanced security measures is lower. In these specific scenarios, Microsoft Defender can be a practical and sufficient solution. But it is important to understand that this depends on the overall context of the business, not just on the tool itself.
The answer depends on your specific situation. There is no single solution that fits every business, and in some cases, Microsoft Defender can be enough.
However, security decisions should not only be based on the current situation, but also on how threats evolve over time. For a deeper look into this, see our analysis: Will Windows Defender still be secure enough in 2026? What businesses should know before relying on it.
The Real Question SMEs Should Ask
Instead of focusing on the question of which antivirus is better, SMEs should take a step back and look at the bigger picture. Comparing tools can be helpful, but it often leads to the wrong focus. Security is not only about choosing the right product, it is about being prepared for real situations. A more important question is what would happen if an incident occurs tomorrow. Would the business understand what is going on, and would it be able to respond immediately and with confidence?
In many cases, the answer is unclear. Not because the tools are missing, but because there is no clear visibility and no defined response process. Systems may generate alerts, but the meaning of these alerts is not fully understood. Decisions take time, and uncertainty slows everything down. This is where the real risk lies. It is not only about whether a threat can be detected, but whether the business can interpret the situation correctly and take the right actions without delay.
If this clarity is missing, the tool itself is not the main problem. Even good tools cannot compensate for a lack of visibility and response capability. Without these elements, security remains reactive and uncertain. For SMEs, the goal should not only be to install protection, but to build a setup that allows them to understand and control a situation when it matters most.
Instead of focusing on the question of which antivirus is better, SMEs should take a step back and look at the bigger picture. Comparing tools can be helpful, but it often leads to the wrong focus. Security is not only about choosing the right product, it is about being prepared for real situations. This is also why relying on tools alone is rarely enough. A deeper perspective on this can be found in our article: Why Virus Protection Alone Is Rarely Enough – and Why Knowledge Is the Key.
Conculsion: Microsoft Defender vs CrowdStrike for small business
The decision between Microsoft Defender and CrowdStrike is not simply about choosing the “better” tool. It is about understanding what your business actually needs in a real-world situation. Microsoft Defender offers solid baseline protection and can be a practical starting point for very small environments. It is easy to use, cost-efficient, and already integrated into most systems. For businesses with low risk and simple setups, this may be enough.
However, as soon as business operations depend on availability, data, and trust, the requirements change. In these situations, visibility, fast response, and the ability to understand an incident become critical. This is where CrowdStrike provides a clear advantage. It is not only designed to detect threats, but to help businesses understand and control them in real time. This makes it a stronger choice for SMEs that want to reduce uncertainty and make better decisions under pressure. In the end, the question is not which tool is more advanced, but which one fits your risk level and your ability to respond when something happens.
For more practical insights and real-world cybersecurity perspectives, feel free to connect with me on LinkedIn




