Many small and medium‑sized businesses try to save money wherever possible. This is completely understandable — especially when economic conditions are uncertain and every expense needs to be justified. As a result, many business owners turn to free antivirus software, assuming it provides “good enough” protection for their company devices and sensitive data. After all, if a tool is free, easy to install, and claims to block threats, why pay for something more? But this assumption can become a costly mistake.
Cybersecurity experts — including well‑known companies like CrowdStrike — have repeatedly warned that free antivirus tools are no longer sufficient to defend against today’s cyber threats. Modern attacks are faster, more sophisticated, and increasingly targeted at small businesses, precisely because they often lack strong security measures. A free antivirus solution that relies mainly on signature‑based detection simply cannot keep up with advanced ransomware, phishing‑driven intrusions, or modern endpoint attacks.
This article breaks down why free antivirus software often falls short for SMEs, the risks that come with relying on it, and the key factors business owners should consider before choosing a security solution.
Why Free Antivirus Software Looks So Attractive
At first glance, free antivirus software can seem like a perfectly reasonable choice for small businesses. The appeal is obvious: there are no monthly subscription fees, installation takes only a few minutes, and the tools promise basic protection against common malware. For many business owners who are trying to keep expenses under control, this combination feels like a win. And to be fair, for private home users who mainly browse the internet, stream videos, or check emails, free antivirus solutions often are sufficient. However, this sense of security can be misleading.
Free antivirus tools are designed with the needs of casual home users in mind — not businesses that handle sensitive data, rely on uninterrupted operations, or face targeted attacks. They typically offer only fundamental, signature‑based detection, which means they can catch known threats but struggle with anything more advanced. In a business environment, the stakes are dramatically higher: a single successful attack can lead to data loss, downtime, financial damage, and long‑term reputational harm.
What looks like a harmless cost‑saving decision on the surface can therefore expose a company to risks that far outweigh the money saved. The reality is that the threat landscape for businesses is fundamentally different from that of private users — and the tools designed for home use simply aren’t built to handle it.
The Threats That Modern SMEs Face
Small and medium-sized enterprises are increasingly in the crosshairs of cybercriminals. This is not a coincidence. Attackers are rational. They go where the effort is low and the reward is high. Large corporations typically invest heavily in security teams, enterprise-grade software, and dedicated IT departments. SMEs, by contrast, often run on lean budgets and may have little more than a free antivirus tool standing between their business data and the outside world. For criminals, this makes smaller companies an easy and attractive target.
One of the most common threats facing SMEs today is phishing. A phishing attack is when a criminal sends a message, usually an email, that looks like it comes from a trusted source. It might appear to be from a bank, a supplier, or even a colleague. The message typically asks the recipient to click a link and enter their login details. Once the criminal has those credentials, they can access company systems, read private emails, steal data, or set the stage for a much larger attack. Phishing emails have become so convincing that even experienced employees are sometimes deceived.
Ransomware is another threat that has caused enormous damage to small businesses in recent years. In a ransomware attack, malicious software is installed on a company’s computers, often through a phishing email or an infected file download. The software then encrypts the company’s files, making them completely inaccessible. The attackers demand a ransom payment, often in cryptocurrency, in exchange for the decryption key. Even businesses that pay the ransom are not guaranteed to get their data back. Recovery can take days or weeks, and the financial and reputational damage can be severe.
Password theft is a closely related problem. Criminals use a variety of methods to steal login credentials. These include fake websites that mimic legitimate services, data leaks from other platforms where employees have reused the same password, and malware that silently records keystrokes. Once an attacker has a valid username and password, they can often move through a company’s systems without triggering any obvious alarms. This type of attack is particularly dangerous because it does not always look like an attack at first.
Many SMEs are also targeted through their financial processes. So-called business email compromise attacks involve criminals impersonating a supplier, a manager, or a senior executive. A convincing fake email is sent to someone in the accounts department, asking them to process an urgent payment or update banking details. These fraudulent invoice attacks are simple in concept but highly effective in practice. Without proper verification processes and security tools that flag suspicious emails, it is surprisingly easy for employees to be misled.
Data breaches represent a different but equally serious category of risk. A breach occurs when unauthorised individuals gain access to confidential information held by a company. This might include customer names, addresses, payment details, or employee records. Under data protection regulations such as the GDPR in Europe, businesses are legally required to report significant breaches and may face substantial fines if they have not taken reasonable steps to protect the data in their care. Beyond the legal consequences, the loss of customer trust that follows a public data breach can be very difficult to recover from.
Finally, the rise of remote and hybrid working has created a new layer of vulnerability. When employees work from home or connect to company systems using personal devices or unsecured Wi-Fi networks, the attack surface grows considerably. Home networks typically do not have the same level of protection as an office environment. A laptop that connects to both a home router and the company network can become a bridge that attackers use to get inside the organisation. Without endpoint protection that covers remote devices, businesses are leaving these entry points dangerously exposed.
What all of these threats have in common is that they are not random or indiscriminate. Cybercriminals research their targets, adapt their methods, and specifically look for gaps in protection. SMEs that rely on basic free antivirus software are, in most cases, leaving significant gaps. That is not a comfortable position to be in when the consequences of a successful attack can threaten the survival of the business itself.
The Biggest Problem: Limited Protection
The most fundamental weakness of free antivirus software is not any single missing feature — it is the underlying philosophy of protection. Most free tools are built around a reactive model: they scan files, compare them against a database of known threats, and flag anything that matches. A decade ago, that approach was largely sufficient. Today, it is not.
The cyber threat landscape has shifted dramatically. Attackers have moved well beyond simple viruses and predictable malware. Modern attacks are carefully crafted, multi-stage operations that are specifically designed to evade the kind of signature-based detection that free tools rely on. A piece of ransomware written last week may not yet exist in any threat database. A phishing email engineered to mimic a trusted supplier will not trigger a file scan. Stolen login credentials used to access your systems quietly from the outside look, to a basic antivirus tool, like perfectly normal activity.
The methods attackers use today are deliberately human-focused. Social engineering — manipulating employees into handing over access, clicking a link, or transferring funds — does not involve malicious files at all. Business email compromise, where an attacker impersonates a colleague or executive, can cause serious financial damage without ever triggering a traditional security alert. Free antivirus software has no meaningful answer to these kinds of threats.
Professional security solutions designed for business environments take a fundamentally different approach. Rather than simply reacting to known threats, they continuously monitor behavior across every endpoint in real time — watching for anomalies, unusual process activity, and patterns that suggest something is wrong, even if the specific threat has never been seen before. This kind of proactive, behavior-based detection is what allows modern security platforms to catch attacks that signature-based tools would miss entirely.
Beyond detection, business-grade solutions offer a range of capabilities that free tools simply do not provide. Dedicated ransomware protection can identify and halt encryption attempts before they cause widespread damage, and recovery tools can help restore systems quickly if an incident does occur. Email security layers intercept phishing attempts and malicious attachments before they ever reach an employee’s inbox — addressing one of the most common entry points for attacks at the source. Firewall management and network monitoring add further visibility into who and what is connecting to your infrastructure, flagging unauthorized access attempts that might otherwise go unnoticed.
One of the most significant advantages of professional platforms is Endpoint Detection and Response, commonly known as EDR. EDR goes far beyond scanning files. It continuously records and analyzes the behavior of every process and application running on your devices, building a detailed timeline of activity across your entire environment. If an attack occurs, that timeline allows security teams to understand exactly what happened, how far it spread, and what needs to be addressed. More importantly, EDR systems are connected to cloud-based threat intelligence networks that aggregate data from millions of endpoints worldwide and update in real time. A new attack technique identified anywhere in the world translates, within hours or minutes, into enhanced protection for every business using the platform.
For SMEs without a dedicated in-house IT security team, this matters enormously. Professional solutions also come with access to expert support — teams that can assist rapidly when an incident occurs, helping to contain damage and guide recovery at the moment it is most needed. That kind of expertise, available around the clock, is something no free tool can replicate.
Taken together, these capabilities are not optional extras for businesses that want a higher tier of comfort. They are practical necessities for any organization that handles customer data, processes payments, or depends on its digital systems to operate. The difference between a free consumer tool and a professional business security platform is not a question of degree — it is a question of whether your defenses are built for the threats that actually exist today.
Watch my video: How to create extremely strong passwords that hackers cannot easily guess
Downtime Can Cost Far More Than Security Software
Many business owners focus only on the upfront price of security software. This is understandable — budgets are tight, and an annual subscription fee can feel like an unnecessary expense when nothing has gone wrong yet. But this way of thinking often leads to a false sense of economy. The real financial risk is not the cost of the software. It is the cost of what happens after a successful cyberattack.
Consider this scenario: ransomware infects your company network. Your files are encrypted and completely inaccessible. Employees cannot work. Customer orders cannot be processed. Emails stop functioning. Your phone lines may depend on internet connectivity — and those go down too. Within hours, your entire operation has ground to a halt. And unlike a power outage or a server failure, a ransomware attack does not simply resolve itself once the lights come back on. Recovery can take days or even weeks.
The immediate costs are obvious: you may face demands for a ransom payment, which security experts and law enforcement agencies universally advise against paying — yet some businesses feel they have no choice. Beyond that, you will likely need emergency IT support to assess the damage, remove the malware, restore systems from backups (if reliable backups even exist), and verify that no data has been exfiltrated. Each of these steps takes time and costs money.
But the less visible costs can be even more damaging in the long run. If your business handles personal data — and almost every business does, even if only in the form of customer email addresses — a breach triggers legal obligations under data protection regulations such as the GDPR. Depending on the nature and scale of the incident, you may be required to notify affected individuals, report the breach to the relevant supervisory authority, and potentially face investigation and fines. For a small business, even a modest regulatory penalty can be a serious financial blow.
Then there is the question of reputation. Clients and customers who hear that your systems were compromised will naturally begin to question whether their data is safe with you. Some will quietly take their business elsewhere. Partners may reconsider working with you. Winning back that trust takes time — often much longer than it takes to clean up the technical damage. In competitive markets, that erosion of confidence can have a lasting impact on revenue.
When you add it all up — lost productivity during downtime, emergency IT recovery costs, potential legal and regulatory exposure, and the long-term cost of reputational damage — even a relatively contained cyber incident can easily run into several thousand euros for a small business. Larger incidents can cost significantly more.
Compared to these figures, the annual cost of professional endpoint protection looks very different. Business-grade security solutions typically cost a fraction of what a single incident would set you back. Viewed through that lens, the question is no longer whether you can afford proper protection. It is whether you can afford to go without it.
Free Antivirus Software Lacks Business Management Features
There is another important area where free antivirus tools fall short: visibility and central management. As a business owner or manager, you need to know what is happening across all the devices in your company at any given moment. This is not just a matter of convenience — it is a fundamental requirement for running a secure operation. Questions like these matter every day:
- Which devices are currently protected and up to date?
- Which systems have outdated software or missing security patches?
- Where has suspicious activity been detected?
- Did any employee accidentally click on a dangerous link?
- Has any device been connecting to untrusted networks or external storage?
- Are all devices running the correct, company-approved security policies?
With free antivirus software, the honest answer to most of these questions is: you do not know. Each device runs its own local installation, with its own settings, its own update schedule, and its own logs. If you want to check the security status of a device, you have to physically sit in front of it — or ask the employee using it. Multiply that across ten, twenty, or fifty devices, and the situation becomes unmanageable very quickly. Vulnerabilities go unnoticed. Updates get skipped. An employee’s laptop that has not received a definition update in three weeks becomes a weak point that attackers can exploit — and you may never know until it is too late.
This lack of oversight is not just an operational inconvenience. It is a structural security gap. In a business environment, the strength of your defenses is only as good as the weakest device on your network. A single unpatched endpoint can serve as the entry point for an attack that spreads across your entire infrastructure.
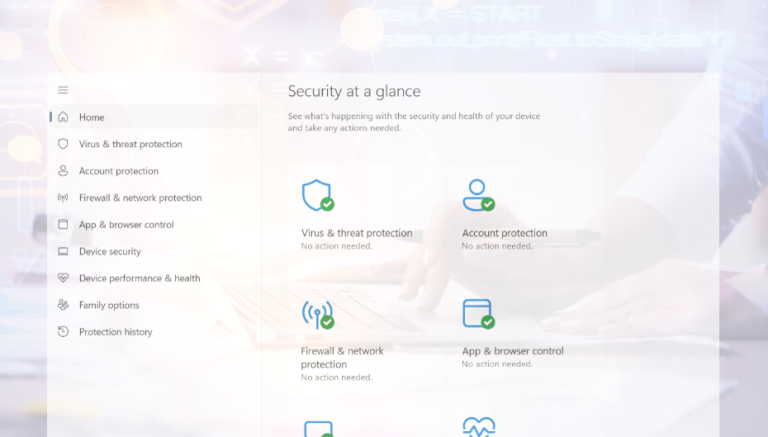
Business-grade security platforms are built specifically to address this problem. They provide administrators with a single, centralized dashboard that displays the real-time security status of every device in the organization. From one screen, you can see which machines are fully protected, which have pending updates, which have flagged suspicious activity, and which may have been exposed to threats. You can push policy changes, trigger scans, and respond to incidents across all devices simultaneously — without leaving your desk.
This kind of visibility also has direct benefits beyond day-to-day security management. If your business is subject to an audit, an inspection, or a client due diligence review, being able to demonstrate a documented, consistently enforced security posture is a significant advantage. Increasingly, larger corporate clients and public sector procurement processes require their suppliers and partners to meet minimum cybersecurity standards. A centrally managed, business-grade security solution provides the kind of verifiable evidence that a patchwork of free tools simply cannot.
For any SME with more than a handful of devices — or with staff working remotely or across multiple locations — the absence of central management is not a minor inconvenience. It is a meaningful gap in your ability to protect your business, your clients, and your data.
What Should SMEs Do?
The right approach for your business will depend on your size, your industry, and the type of data you handle. There is no single solution that fits every situation. However, there are some clear, practical steps that nearly every SME can benefit from — regardless of where you are starting from.
Before you can protect your business, you need to know what you are actually protecting. Make a list of every device that connects to your network or handles business data: laptops, desktop computers, smartphones, tablets, servers, and any cloud services or third-party platforms your team uses regularly. Do not overlook devices that employees use for both work and personal purposes — these are often the least secured and among the most common entry points for attackers. Remote workers add another layer of complexity, as their home networks and personal devices may not meet the same standards as your office infrastructure. A clear picture of your digital footprint is the essential first step toward securing it.
Not every business holds the same kind of data, but almost all businesses hold something worth protecting. Customer contact details, payment records, contracts, supplier information, employee data, and confidential business communications are all valuable — both to your business and, unfortunately, to attackers. Take a moment to consider what the consequences would be if that data were stolen, encrypted, or made public. Would you face regulatory obligations? Would clients leave? Would your business be able to continue operating during a recovery period? Once you frame the question in terms of risk rather than cost, the case for proper protection usually becomes much clearer.
Many small businesses rely on whatever security software came pre-installed on their devices, or use free consumer tools that were set up years ago and rarely revisited. These solutions may offer some protection, but they are almost certainly not configured for a business environment, not centrally managed, and not keeping pace with the current threat landscape. It is worth taking the time to review what you currently have in place and asking honestly whether it would hold up against the kinds of attacks that are targeting businesses like yours today.
You do not need to navigate these decisions alone. A qualified IT security specialist or managed service provider can assess your current setup, identify the most significant gaps, and recommend solutions that are appropriate for your size and budget. Many professional security platforms are available at a transparent cost per device per month, making them far more accessible than many business owners assume. Some vendors also offer specific pricing tiers designed for small and medium-sized businesses, so it is always worth asking. The conversation costs nothing, and the insight you gain can be genuinely valuable.
Even the best security software is only part of the picture. Equally important are regular software updates, strong password practices, multi-factor authentication, and basic staff awareness training. Many successful attacks do not exploit technical vulnerabilities at all — they exploit human ones. An employee who recognizes a phishing email and knows not to click the link is one of your most effective defenses. Building a basic culture of security awareness within your team, combined with the right technical tools, gives your business a much stronger foundation than any single product can provide on its own. The investment required to protect a small business properly is, in most cases, far more modest than people expect. And when weighed against the potential cost of a serious incident, it is almost always money well spent.
Conclsusion: Is Free Antivirus Software Enough for Small Businesses?
Free antivirus software can provide a basic layer of protection and is certainly better than nothing — but for small businesses, it falls well short of what a serious security posture demands. The threats facing businesses today go far beyond simple viruses: ransomware, phishing campaigns, credential theft, and supply chain attacks require layered defenses that free tools simply aren’t designed to deliver.
What free solutions lack is not just features, but context. They typically offer no centralized management, no endpoint detection and response (EDR), no policy enforcement, and no support when something goes wrong. For a solo freelancer, that may be an acceptable trade-off. For a business handling customer data, processing payments, or relying on operational continuity, it is a significant liability.
The cost of a breach — in downtime, data loss, reputational damage, and potential regulatory fines — almost always far exceeds the annual cost of a proper business security solution. Investing in paid, business-grade protection is not a luxury; it is a baseline responsibility.
Want to protect your business better against modern cyber threats? Join my Slack community and connect with business owners, IT professionals, and cybersecurity enthusiasts. Get practical security tips, threat warnings, and real-world advice to help keep your company safe.
👉 Join the Slack Channel now and stay one step ahead of cybercriminals
I also recommend to read the following articels:
Will your company still need antivirus software in 2026 – or is it just expensive snake oil?
Why Virus Protection Alone Is Rarely Enough – and Why Knowledge Is the Key